In 2024, the HHS Office for Civil Rights (OCR) settled with a regional health system for $1.3M after a breach affecting 360,000 patients. The settlement order specifically called out the covered entity's failure to update its Notice of Privacy Practices in a timely manner after a workflow change in 2022 that introduced new uses and disclosures of protected health information. The notice on the website at the time of OCR's investigation reflected the pre-2022 workflow. The covered entity could not produce evidence that the website notice had been updated to reflect the new uses, or that members of its workforce had been notified.
HIPAA is generally thought of as a clinical and IT regulation, but a substantial portion of compliance obligation lives on the public web. The Notice of Privacy Practices (NPP) is required to be posted on a covered entity's website. Breach disclosures for breaches affecting 500 or more individuals are required to be posted on a prominent location of the website. Business Associate Agreements (BAAs) are not posted on the public web, but the vendor side of the relationship publishes operational changes (sub-processor lists, security pages, certifications) that bear directly on whether the BAA terms are still being met.
For covered entities and business associates, the practical implication is that the website is part of the compliance surface, and so is every business associate's website. Manual quarterly review does not catch the changes that matter most, including the changes that will be cited in the next OCR enforcement action.
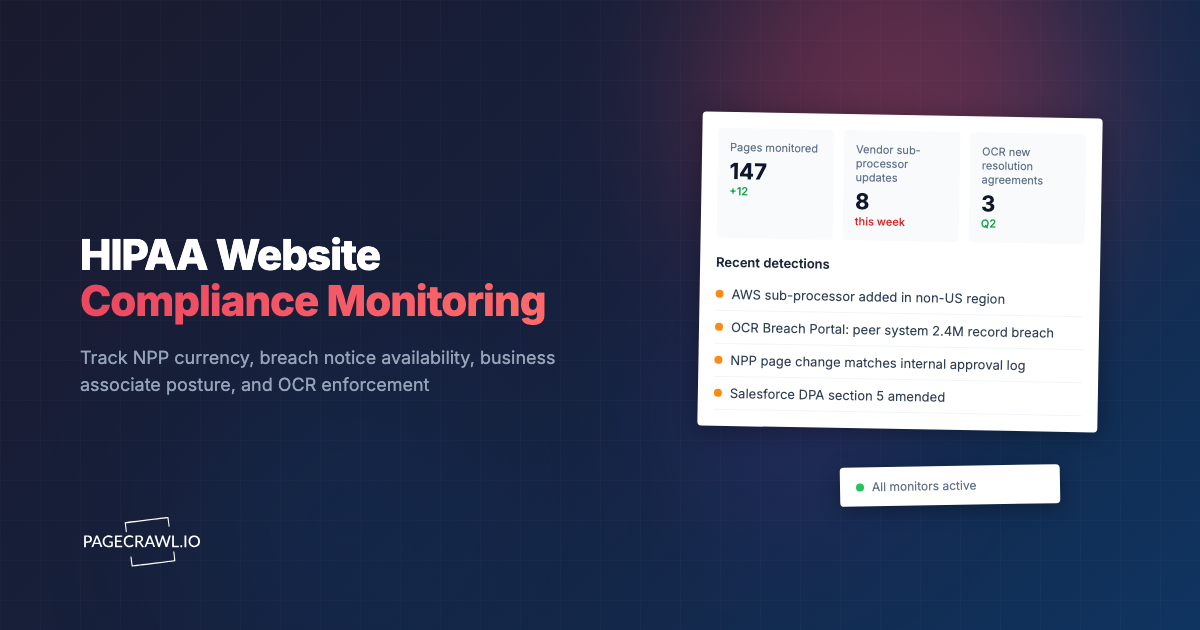
This guide covers what HIPAA requires for web content, what to monitor on your own site and on business associate websites, how to track OCR enforcement and HHS guidance, and how to set up the monitoring tooling without dedicating a full headcount.
What HIPAA Requires for Web Content
HIPAA requirements relevant to web monitoring sit across the Privacy Rule (45 CFR Part 164 Subpart E), the Security Rule (Subpart C), and the Breach Notification Rule (Subpart D).
Notice of Privacy Practices
45 CFR 164.520 requires covered entities to publish their NPP and to make it readily available. For covered entities that maintain a website with information about customer services or benefits, the NPP must be prominently posted on the site, and must reflect the entity's current uses and disclosures of PHI.
The substantive obligation is that the NPP on the website matches the actual practices of the covered entity. When the covered entity introduces a new use or disclosure (a new electronic health record vendor, a new analytics partner that handles PHI, a new patient engagement platform), the NPP must be updated. If the website NPP lags actual practice by weeks or months, the entity has a documented Privacy Rule deficiency.
The monitoring implication is that any change to the entity's data flows is a trigger to review and potentially update the website NPP, and the timeline of the website update has to be defensible.
Breach Notifications
45 CFR 164.404 through 164.408 cover breach notification obligations. For a breach affecting 500 or more individuals, the covered entity must notify HHS, must notify prominent media outlets in the affected state, and must provide notice on a prominent location of its website for 90 days.
The 90-day notice requirement is a website obligation. Failure to maintain the notice for the required period, or failure to retain a record of the notice having been posted, is a discrete violation distinct from the underlying breach.
Business Associate Agreements
A BAA is a contract between the covered entity and the business associate. It is not posted on the public web, but it depends on the business associate's continuing operational practices. The BAA typically obligates the business associate to maintain specific safeguards, to use and disclose PHI only as permitted, to report breaches, and to provide subprocessor controls.
When the business associate changes its security posture, adds a new subprocessor, loses a certification, or experiences a breach, the BAA terms may be triggered. Most business associates publish these changes on their trust portals, security pages, or status pages. The covered entity that monitors these sources is in a position to detect a BAA-relevant change before it becomes a breach. The covered entity that does not monitor finds out from the trade press or from OCR.
HHS and OCR Publications
OCR maintains the public Breach Portal at ocrportal.hhs.gov/ocr/breach. Every breach affecting 500 or more individuals is posted here. The portal is searchable by covered entity, year, and breach type. For risk benchmarking and peer comparison, the portal is a primary source.
OCR also publishes resolution agreements, civil monetary penalties, and corrective action plans. These describe in detail the failures that resulted in enforcement, and are the most useful predictor of where OCR will focus enforcement next.
HHS publishes HIPAA guidance and FAQs at hhs.gov/hipaa. These are updated continuously as new technologies emerge (cloud computing, mobile health, AI in healthcare) and as enforcement priorities shift.
What to Monitor for HIPAA Compliance
The pages worth tracking divide into three groups: your own site, your business associates, and the regulator.
Your own website
The published NPP page. Detect any change. A change should match a corresponding internal record of NPP updates approved by the privacy officer. A change without an internal record is a process deficiency.
The breach notice page. During an active breach notice obligation, monitor the page to confirm continuous availability for the required 90 days. Capture timestamped evidence of posting and continued availability.
The contact and patient rights pages. Patient rights under 45 CFR 164.522 (request restrictions, request confidential communications, access to PHI, amendment, accounting of disclosures, complaints to OCR) are required to be communicated. The pages communicating them are part of the compliance surface.
Business associate websites
Sub-processor lists. Business associates that operate as cloud or SaaS providers typically maintain a sub-processor list. New sub-processors trigger evaluation under the BAA's permissible use provisions. Examples include AWS at aws.amazon.com/legal/sub-processors, Microsoft at m365hipaa.azurewebsites.net (or the relevant Microsoft subprocessor page), and Google at workspace.google.com/terms/dpa_terms.html.
Trust portals and security pages. Loss of a SOC 2 Type II attestation, a HITRUST CSF certification, or an ISO 27001 certification is a posture change that may affect the BAA's safeguards expectations. Trust portals at trust.{vendor}.com or compliance.{vendor}.com publish certification status.
Status pages and incident postmortems. Incidents at business associates can become breaches at the covered entity. Status pages typically post the operational notice; postmortem RCAs typically post the security analysis.
BAA and DPA pages. Many business associates publish their standard BAA and DPA online. Changes to the standard agreement are leading indicators that the executed BAA may need to be re-papered.
Authentication and access logs. Some business associates expose customer-facing authentication logs and configuration pages. Changes to MFA requirements, IP allowlists, or session timeout defaults can affect Security Rule safeguards.
OCR and HHS
OCR Breach Portal. Monitor for new entries by covered entity name (your own and your peers'). Monitor for entries citing your business associates so you have early notice of issues that may affect your relationship.
OCR resolution agreements. Newly posted resolution agreements describe the failures OCR found, the corrective action plans imposed, and the financial penalty. The first read on enforcement priorities.
OCR civil monetary penalty notices. When OCR proceeds to a formal enforcement order, it is published. CMPs are rare but signal a hardening of OCR position on a specific issue.
HHS guidance pages. HIPAA FAQs, clarification statements, and emergency guidance updates. Continuous tracking is cheap and the alerts are infrequent.
State attorney general HIPAA pages. Several state AGs (California, New York, Washington, Connecticut) actively enforce HIPAA in coordination with OCR. State AG enforcement publications are useful supplementary signal.
Setting Up HIPAA Monitoring
The pattern that scales for covered entities and business associates is a continuous monitoring system that detects changes across all three categories, routes alerts to the privacy and security teams, and produces a compliant audit trail.
Build the inventory
Walk your own site and identify the NPP page, breach notice page, contact and patient rights pages, and any other pages that communicate Privacy Rule obligations. Tag each as #our-site.
List your business associates. For each, identify the sub-processor list page, the trust portal, the status page, the BAA template page, and any other pages that affect the BAA. Tag each as #vendor:{name} and by artefact type.
List the OCR and HHS pages you track. Breach Portal, resolution agreements, CMPs, guidance pages. Tag as #regulator:ocr or #regulator:hhs.
Set capture frequency
Your own NPP and breach notice pages: hourly during active breach notice periods, daily otherwise. Business associate trust portals and sub-processor pages: daily for critical vendors, weekly for monitored-only. OCR Breach Portal and resolution agreements: daily. HHS guidance: weekly.
Tell PageCrawl what your entity looks like
Workspace instructions describe the covered entity's profile. "Regional health system, 12 hospitals, 4 million annual encounters, primary EHR Epic, key business associates Salesforce, AWS, Twilio, Datadog. Active sensitivities: AI tools handling PHI, telehealth platforms, third-party analytics partners with potential PHI exposure." This biases AI summaries to highlight what matters for that profile.
Route to the right team
Privacy team gets NPP changes, OCR enforcement updates, and business associate BAA template changes. Security team gets sub-processor changes, certification changes, and incident postmortems. Legal team gets resolution agreements and state AG enforcement. Use per-tag default channels.
Maintain the audit trail
Every detected change is timestamped with before/after snapshots and full archives. For NPP changes specifically, the audit trail of detected change should match the internal approval record. For breach notice availability, the change history demonstrates continuous posting throughout the 90-day requirement.
PageCrawl Ultimate-plan archives are captured as WACZ files carrying multiple independent cryptographic attestations: an embedded WACZ Auth signature, plus three sidecar timestamp proofs (an OpenTimestamps Bitcoin anchor and two RFC 3161 timestamps from independent commercial Trust Service Providers). When OCR investigators ask for the version of a Notice of Privacy Practices or breach notice as it appeared on a specific date, the response is a single signed public verification link. The investigator opens the link, sees the manifest hash and every cryptographic attestation, and verifies the proofs against public certificate chains and the Bitcoin blockchain without needing a PageCrawl account or access to the covered entity's internal systems. Aligned with FRE 902(13)/(14) self-authenticating evidence in any subsequent litigation.
The AI fabrication problem
In 2026 a generative model can produce a plausible screenshot of a Notice of Privacy Practices or breach notice page in seconds. A self-stored screenshot proves nothing to an OCR investigator because the covered entity could have generated it after the fact. What AI cannot fabricate is a hash anchored to the Bitcoin blockchain, an RFC 3161 timestamp signed by a Trust Service Provider's private key, or a qualified seal from a regulated QTSP. PageCrawl attaches several of these in parallel on every detected change, so the archive's existence at a specific moment is attested by parties the covered entity does not control. That is the only practical evidentiary standard for HIPAA records in an AI-saturated world.
A Worked Example: Sub-Processor Change at a Cloud Vendor
A common pattern: AWS posts a sub-processor list update adding a new geography for a service the covered entity uses for PHI. The notice is dated and goes live without prior email notification. Under the BAA, the covered entity has obligations to evaluate the change against its data residency commitments to patients.
Without continuous monitoring, the covered entity finds out at the next quarterly vendor review, which may be six weeks after the change went live. During those six weeks, PHI may be processed in the new geography in ways that the covered entity has not yet evaluated.
With continuous monitoring, the change is detected within hours of posting. The AI summary highlights the new geography and the affected service. The vendor management team triggers the evaluation under the BAA. The privacy team determines whether the NPP needs to be updated to reflect any change in cross-border transfer practices. The audit trail shows that the covered entity acted within days of the change, not weeks.
Common Pitfalls
Forgetting that the website is part of the compliance surface
NPPs, breach notices, and patient rights pages are required communications. When the website lags actual practice, the covered entity has a documented deficiency. Continuous monitoring of the entity's own pages is just as important as monitoring vendor pages.
Skipping the small business associates
Major cloud vendors get attention. Smaller business associates (specialty SaaS for billing, scheduling, patient engagement) often do not. The smaller vendors are also where unmonitored sub-processor changes most commonly become breaches. Coverage needs to extend to every BAA, not just the top five.
Treating OCR enforcement as historical reading
OCR enforcement actions are leading indicators of where enforcement focus will go next. A resolution agreement citing inadequate NPP updates means OCR is focused on NPP currency across the sector. Treating these as background reading rather than enforcement signal misses the warning.
Manual quarterly reviews
Quarterly cadence misses changes that happen between reviews. By the time the next review surfaces the change, the timing of the entity's response is no longer defensible. Continuous capture closes the gap.
No retention
A monitoring system that does not retain captured snapshots is not useful for OCR investigations. Investigators ask for the version of a specific page on a specific date. Without retention, the answer is "we cannot produce that record."
Choosing your PageCrawl plan
PageCrawl's Free plan lets you monitor 6 pages with 220 checks per month, which is enough to validate the approach on your most critical pages. Most teams graduate to a paid plan once they see the value.
| Plan | Price | Pages | Checks / month | Frequency |
|---|---|---|---|---|
| Free | $0 | 6 | 220 | every 60 min |
| Standard | $8/mo or $80/yr | 100 | 15,000 | every 15 min |
| Enterprise | $30/mo or $300/yr | 500 | 100,000 | every 5 min |
| Ultimate | $99/mo or $999/yr | 1,000 | 100,000 | every 2 min |
Annual billing saves two months across every paid tier. Enterprise and Ultimate scale up to 100x if you need thousands of pages or multi-team access.
Compliance monitoring is the cheapest insurance you can buy. A single missed regulatory change can trigger fines in the tens or hundreds of thousands, not to mention the audit overhead of proving you did not see it coming. Enterprise at $300/year covers 500 regulatory pages with unlimited history and timestamped screenshots, which is usually exactly what an assessor wants to see. All plans include the PageCrawl MCP Server, so your compliance team can ask Claude to summarize every change to a specific regulation over the last quarter and pull the exact diff, turning your monitoring history into a queryable audit trail. Paid plans unlock write access so AI tools can create monitors and trigger checks through conversation. Standard at $80/year is enough to cover 100 pages across your primary regulatory bodies if your program is smaller.
Getting Started
Set up HIPAA monitoring in three steps:
- Inventory the pages. Your own NPP, breach notice, and patient rights pages. Every business associate's sub-processor list, trust portal, and status page. The OCR Breach Portal and resolution agreement page.
- Tag and route by team. Privacy team for NPP and OCR enforcement. Security team for vendor sub-processors and certifications. Legal team for resolution agreements and state AG enforcement.
- Set workspace instructions describing your entity profile so AI summaries highlight what matters for your covered-entity scope, your business associate stack, and your sensitivities.
For related reading, see DORA compliance monitoring, SaaS sub-processor list monitoring, and GDPR and CCPA change tracking.
If your covered entity is building a continuous HIPAA monitoring program, the Compliance Monitoring use case walks through the full setup with audit-trail conventions, workspace instructions, and per-team alert routing for privacy, security, and legal functions.